Managed SIEM
Interpreting information
Sometimes everything is actually already there! This is the case with log files, which comprehensively document what happens in your IT systems. Use these sources of information to immediately detect attacks, unusual patterns or dangerous trends and react in a targeted manner - with a managed SIEM solution for your log management. In our Security Operations Centre (SOC), we monitor your systems and evaluate the risks for you.
What is a SIEM?
The abbreviation SIEM stands for Security Information & Event Management. Behind it is a software-based technology with which companies discover security gaps via log file analysis and ward off attacks in good time. The aim is to strengthen their security and meet compliance requirements. The basis of a SIEM solution are the log files, i.e. the data that log all processes in the systems and networks of a company - similar to a flight recorder. Typical sources for the SIEM are PCs, laptops and notebooks, servers, routers and switches, virus scanners, firewalls, web servers and other network and IT security components. For log file analysis, the SIEM software brings all information together centrally. From there, the data is analysed with a focus on the detection of cyber attacks.
Detect gaps intelligently
When analysing log files, the SIEM uses intelligent analysis tools such as correlation models and artificial intelligence. This means that relationships between the data are established and evaluated to identify anomalies. An example: The log files show that your employees log into the respective systems when they start work. If someone makes a typing error and enters their password again, this is classified as compliant with the rules. The situation is different if several password attempts are made within a very short period of time. Such a brute force attack would be detected by the SIEM and trigger an immediate alarm.
- more cyber security through protection against unauthorised access and hacker attacks
- Immediate alerting in the event of an incident
- Strict compliance guidelines (including DSGVO, BSDG, SOX) are met
- Transparent cost model on request: licence costs based on number of log sources
- Different SLA levels possible depending on customer requirements
- Use cases and compliance reports tailored to the customer's needs
- European product if required (DSGVO-compliant)
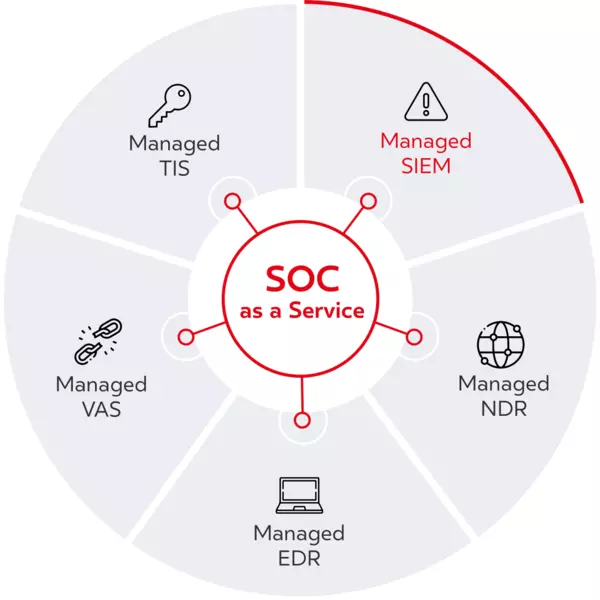
Relief for you: Managed SIEM in the SOC
More security, better compliance management - and more room for your employees: With Managed SIEM, we take over the implementation and operation of the SIEM solution for you. The whole thing is implemented in the BSI-certified dacoso SOC via a central and multi-client-capable SIEM platform, which is managed by our SOC experts around the clock. The collected log files are either processed directly in the customer network or alternatively in the highly secure dacoso data centre.
Our Managed SIEM solution supports the connection of numerous log sources such as:
In our SOC, which is certified by the German Federal Office for Security (BSI), we use an EAL3-certified SIEM solution if required. This meets even the high requirements for cyber security, such as for operators of critical infrastructures as well as in sectors such as defence and aerospace and intelligence services. All evidence for corporate compliance such as DSGVO, PCI-DSS, HIPAA, SOX, etc. can be provided through the use and operation of the SIEM solution.

